Presentation at the European Energy Law Seminar 2022
As presented on the 24th of May 2022 at the European Energy Law Seminar 2022 organized by the Dutch Energy Law Association (NeVER), in cooperation with the University of Groningen’s Centre of Energy Law and Sustainability and the University of Oslo’s Scandinavian Institute of Maritime Law
So before we delve into the fascinating relation between cybersecurity and the worlds of oil, gas, energy and electricity, I need to introduce myself a bit.
I’m a long term computer programmer and entrepreneur. I’ve spent a lot of quality time with intellectual property and M&A lawyers, but I’ve also helped draft legislation, both during my time within Dutch intelligence, but also later as an outsider on behalf of Internet organizations.
These days, I am a member of the ex-ante regulator of the Dutch intelligence and security services. This regulator is staffed with judges and legal people, but I am the special technical member. My role there is to rule on the legitimacy of hacking and surveillance operations but perhaps more important, to make sure that the entire committee understands all the issues, so they know how to weigh the proportionality and subsidiarity of the proposed surveillance or hacking measures.
In this way, I spend a lot of time on information security and cyber operations, but I also live in your world of legislation and laws.
Lately, I’ve been delving deeper into gas and electricity, and perhaps indirectly that has led to me contributing to your conference.
Oil, gas, electricity
My background is mostly in telecommunications, and there we pride ourselves on being 100% available. This even used to have a name ‘dial tone reliability’. We’re no longer delivering on that though. 5 minute outages are the norm now, and sometimes things break for whole days. The telecommunication industry has mostly outsourced itself, with most “telcos” no longer being actual telecommunications companies. Instead they are hubs of contracts & financing operations.
A sound powered phone, the ultimate in reliability

Modern phones on the desk of Joe Biden, each a complicated computer
The world of oil & gas and electricity has been very refreshing to me - 5 minute outages still make the news here. Such things have to be reported and they attract serious attention. I’ve also found the people working here to be very dedicated, and the engineers are proud of what they do. They also communicate robustly and clearly.
One thing I have noted more broadly however is that people in legal and policy do not have a lot of honest down to earth contact with the world of cyber. And in theory, there would also be little need for such contact. This would be true if computers and networks were actually secure and we could write down that parties undertake to properly protect their networks and use certified secure solutions, and that this would work.
But the the thing is.. we don’t know how to do any of that.
In this presentation, I want to cover three things:
- The state of cyber is terrible, yet it runs everything
- You can order certified equipment and materials for gas and electrical usage, there are known ways to deliver reliable services safely
- But there is nothing like that for cyber
- We do however know how to do industrial safely, with relatively minimal use of computers and no connectivity to the outside world
- The walls between such operational IT and “normal computers” are crumbling however
- Compare how well your office IT works (‘mostly’) and a refinery (‘would explode otherwise’)
- Office IT reliability and ’the cloud’ are coming for your electrical power plant!
- Legal has powerful toolboxes to deal with financial issues and counter-party risks
- But there are no such equivalents for cyber security
- Since industrial IT is at ever greater risk of normal IT problems, this is a challenge
- Intimate connectivity between IT systems from suppliers and consumers is exposing everyone to problems
- ‘The cloud’ exacerbates this further
- And who will be responsible for that?
The state of cybersecurity
So, just how bad is the state of cybersecurity? Every week, large software vendors release hundreds of fixes for phones, computers and software. Now, this sounds nice, surely things must be getting better. The problem is, the flow of fixes is not in any way decreasing. There must be tens of thousands of unfixed problems since every week we find hundreds more that needed to be addressed. It seems likely new problems are also being added at the same rate.
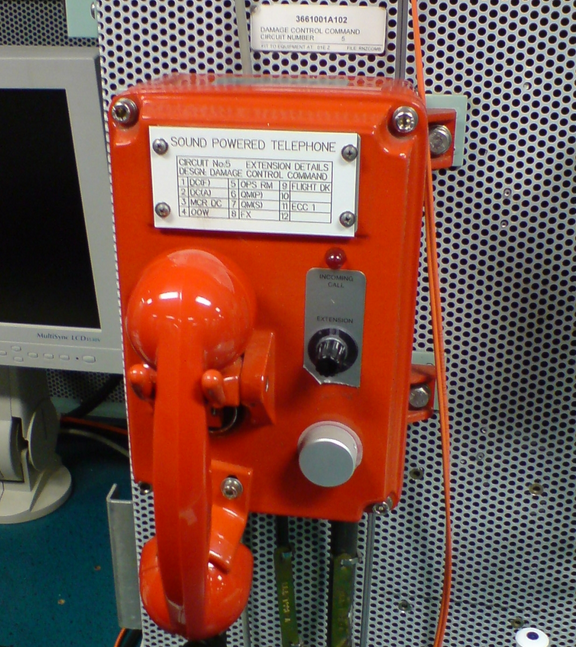
As an example, only a few years ago, it was found you could log in to an Apple laptop by choosing user ‘Other’ and then pressing enter for the password. That was it. The fact that we barely remember this incident tells us a lot about the expectations that we have.
Very relevant for this presentation was the 2021 ransomware attack on the US Colonial Pipeline which caused significant disruption. 87% of gas stations in Washington DC ran out of gas, for example. The actual impact of the attack was only on the billing system, the shutdowns were a precautionary measure. This was not a sophisticated attack.
Another famous case was the Russian attack on the Ukrainian grid in 2015. 230,000 households lost power for between 1 and 6 hours. The Russian attackers were intimately familiar with the Ukrainian infrastructure, which was also very badly maintained. Despite this, the impact of the attack was more symbolic than real.
Earlier this year, European oil facilities were hit by attacks. IT systems were disrupted at Oiltanking in Germany, SEA-Invest in Belgium and Evos in the Netherlands. Again, the eventual impact was limited, as these attacks mostly hit administrative systems.
An important reason why these three attacks did not get very far is that they did not sabotage the industrial infrastructure. Traditionally, industrial computing systems have been very different from office IT administrative systems. Also, these industrial components are typically not connected to public networks.
Industrial IT systems
The best described attack on industrial infrastructure is the infamous 2010 ‘Stuxnet’ operation on Iran’s Uranium centrifuges, aimed at “programmable logic controllers (PLCs)”, Stuxnet specifically targeted Siemens supervisory control and data acquisition (SCADA) systems. This was a very sophisticated attack that managed to make the jump from the outside world to otherwise unconnected industrial networks, where it physically harmed or destroyed over a thousand machines.
 Then president Mahmoud Ahmadinejad during a tour of centrifuges at Natanz in 2008
Then president Mahmoud Ahmadinejad during a tour of centrifuges at Natanz in 2008
Stuxnet was the work of several highly skilled nation states, and the result of over five years of efforts. One reason why it was so hard to do is the physical separation between connected networks and industrial machinery. A second reason is how different such industrial PLCs are from the computers most attackers have experience with.
The effect of Stuxnet was devastating and long-lasting, but it took a lot of work.
A somewhat comparable incident happened recently where, just before Russia invaded Ukraine (again), Russian hackers managed to attack the Viasat satellite communication system, used heavily in wind farms and also by the Ukrainian military. Tens of thousands of satellite modems were attacked, and had their internal ‘firmware’ overwritten, permanently disabling them. The effect was the same as if the modems had been physically destroyed. This was possible because the attackers were able to reach the industrial internals of the modem, and achieving a permanent ‘kinetic’ effect.
Office IT
Now, recall how bad the state of “Office IT” security is, receiving vital security updates every week for issues that had been there for years.
Office IT is moving into the industrial scene.
It is more and more likely that industrial components are “normal computers” now. In addition, it is also less and less accepted that these networks are not connected to other networks or the outside world in general.
Outside attackers are very good at hacking office IT computers, especially if they aren’t updated frequently.
Laptops and phones can easily be rebooted or restarted to install security updates. But any upgrade or restart in an industrial setting requires lots of planning and scheduling - we can’t shut down a refinery on a whim!
As a result, many industrial systems very rarely receive security updates, and many of them run on extremely outdated software. For someone coming from office IT, industrial IT systems look a lot like museums.
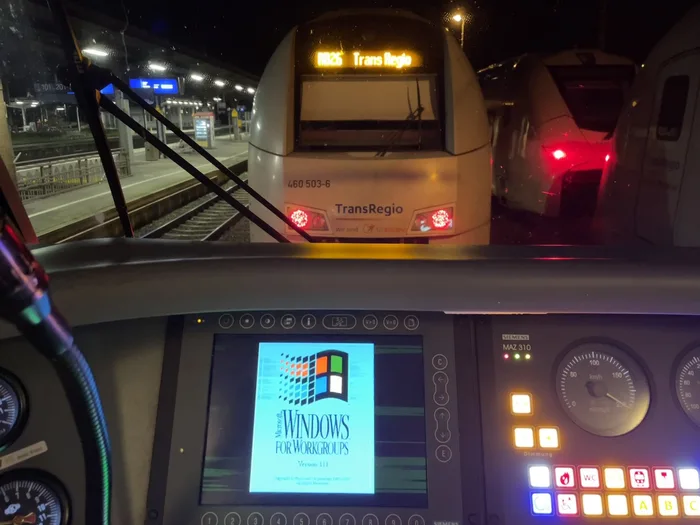
2022 photo of a German train running Windows 3.11 (last update November 8, 1993)
Now, this does not necessarily need to be a problem, as long as such unpatched systems can not be reached from the outside world.
These days, industrial collaborations, outsourcing and the demand for convenience make it ever more likely that your power plant can be accessed from the CFO’s couch. I’ve personally provided mental support to people working on the Uniper Maasvlakte Power Plant 3 (MPP3) who lost the fight and had to see the industrial networks being connected to the outside world.
This leads to the terrible situation that outdated office IT equipment is now powering industrial systems, while also no longer being isolated from attackers.
Cyber immaturity
Cybersecurity and IT in general are very immature fields. If we want to build a safe refinery, there are regulations and tables that tell us what to do. Which temperatures and pressures are tolerable, how thick should the pipes and pressure vessels be. There are inspectors that know what to inspect, there is equipment that is rigidly certified to function properly in specific circumstances.
In the field of IT we just pretend to have these things. We do certify staff, for example, and sometimes this is useful. We however do not have any standards to certify against. We don’t know what a “safe” firewall looks like. We don’t know what kind of monitoring is sufficient to detect hackers. In addition, none of the equipment we work with is reliable.
In short, it is not possible right now to say “we’ll provide guaranteed safe and effective IT solutions”.
It is however very possible to not do so, and we can guard against that.
For example, not installing patches and fixes in a timely manner makes systems far more vulnerable than they have to be. Not monitoring for anomalous network activities means you’ll never detect an attack before it is too late. Making vulnerable systems accessible from the CFO’s couch (even indirectly) will always be an unnecessary risk.
These things can well be addressed and form part of (contractual) security undertakings.
An additional problem here is the rampant outsourcing of services. This frequently means outside parties need access to your network and systems, thus exposing you to any hackers present on your partner’s networks.
Finally, as noted, “Office IT” systems are coming ever closer to industrial systems. In the world of Office IT, it is becoming increasingly exceptional to have any computing equipment on-premise. Instead, services all live “in the cloud”, ie, on other people’s computers. For payroll processing and other fun non-operational activities, this may actually improve security. However, many IT systems are by now ONLY available in the cloud, and can no longer operate independently from the outside world. This again is a risk factor for industrial IT systems: it may no longer be possible to isolate vital equipment from the Internet.
Risk, financial and otherwise
Now, in your field, risk is also the name of the game. I once spoke to a lawyer when I got married, and I wanted to get the formalities over with. But he told me their motto “you are thinking about getting married, we’re already thinking about your divorce”. This was not happy news. 18 years later, I’m still married by the way.
But similarly, in your world, the contracts do not get written just in case everything goes as intended. The contracts come out when things go wrong. If payment dates are missed, what happens? If success of the project truly is contingent on payments, escrow facilities are available. For ongoing arrangements, credit risks can be insured against. Instruments like credit default swaps help protect you against counter-party risks. We rely on a whole auditing infrastructure present within all major (financial) players so this field can function (although we must all remember Enron!).
Similarly, when buying or selling oil, gas, or electrical power, we have mechanisms in place for what happens in case delivery does not happen, or is not of the right quality. For electrical power, explicit reserve operations are in place and contracted for to deal with failures.
But not in cyber
Now, you can see where this is going, similar mechanisms need to be established for IT operations and the risk of cyber attacks. For a long time, such risks could be mitigated or filed under regular “plant safety” controls. But now that the barriers between the outside world and industrial IT are disappearing, and industrial IT is starting to look more and more like the generally unreliable and uncertifiable computing systems we all depend on, it is no longer possible to “hope for the best”.
“We in cyber” are well aware of these problems, but most of us are far too busy making money out of this dire situation to spend much time on actual solutions. And this is where you come in. If the true risk of computer problems, outsourcing and the cloud were to be known and addressed in contracts, many trade-offs would happen differently. Perhaps the CFO can do without realtime figures from his couch.
With this, I hope to have given you some pause for thought next time you encounter a paragraph where appropriate and proportionate measures are promised, but there are no further words on what happens if this turns out not to have been the case. I also hope to have frightened you about the state of IT security, but I think many of you were already aware that things are not good. The frightening bit is that the reliability of Outlook is coming for your nuclear power plants, refineries and LNG terminals.
To round this off on a positive note, there are a few things you can do today. When formalising a partnership, be sure to mandate that suppliers undertake to install security updates in a timely fashion, or where they can’t do so, make sure to disconnect systems from the outside world (entirely).
In addition, be aware that devices like data diodes are available to export data from otherwise isolated networks. These too can be mandated in legal agreements.
I hope this will help you be ahead of the curve & adjust your practices ahead of time!