GNSS Jamming and Spoofing, aka Galileo's Authentication Algorithm Part 3
Welcome to part 3 of my series on OSNMA, the proposed Galileo Navigation Message Authentication protocol. This part can be read independently from part 1 and part 2, but it might be useful to read the introduction to part 1.
This post attempts to explain GPS (GNSS) jamming and spoofing, so it might be a useful read even if you don’t care about Galileo or its authentication.
As usual, I’ve been helped tremendously by Daniel Estévez & many other researchers and Galileo professionals, and again I am very greatful for all the links, corrections, suggestions and knowledge you provided. In a better world I could all thank you by name, but you know who you are.
Threat model
Whenever we attempt to secure something, it is tempting to rush straight to the clever techniques we want to use. It turns out however that it is vitally important to spend serious time on the question: what are we defending against whom?
Although I am sure Galileo designers spent time on it, it appears there are no public papers on the OSNMA “threat model”.
There is quite some literature on GNSS jamming and spoofing, but it is a surprisingly unpopular thing to be talking about in Galileo or GPS circles. A few years ago, I very briefly got involved with the field of Electronic Warfare, which deals with military radio transmissions, radar and other over the air systems.
To my huge surprise, the open literature there is very explicit. You can go out and buy EW 104: EW Against a New Generation of Threats for example and end up well versed in the theory of radar jamming and spoofing.
No such luck for GNSS it appears, or at least, not for OSNMA. Some very good thoughts can however be found in Increasing International Civil Aviation Resilience, authored by the European Commission, Stanford, MITRE, the FAA and the German space agency DLR.
Late 2019 I attended a conference by the Hydrographic Society Benelux on GNSS interference and spoofing where several suppliers and government people explained the field. This post reflects what I learned there.
Jamming, Spoofing, Spoofing detection, Spoofing mitigation
We use GNSS because we want to know where we are, where we are going and what time it is (Position, Velocity, Time, or PVT). In an ideal world this works all the time, and it would be great if technology could make this happen. Sadly, things do break, intentionally and unintentionally.
There is a hierarchy of problems though. When someone jams GNSS, it plain doesn’t work (“denial of service attack”). This actually is the least worst outcome for most scenarios. If GNSS just stops working, there is always something we can do. For example, an airplane that is landing based on EGNOS/WAAS and GPS will abort the landing at that point.
Military solutions will fall back to inertial, celestial or optical guidance, and people using GPS for navigation will at worst show up where they need to be somewhat later than planned.
Spoofing is far far more dangerous. If we manage to make a receiver think it is somewhere else than where it actually is, very bad things can happen. A plane might attempt to land below the runway, an oil tanker might sail straight into the arms of a hostile navy, bombs might fall in the wrong place. The terrible scenarios just write themselves.
We’d love to prevent spoofing, but one of the most important things we can do is simply detect that we are being spoofed, and no longer trust our receiver. This effectively turns spoofing into jamming, which is far easier to deal with.
In other scenarios, it might be possible to detect spoofing signals and selectively ignore them, so we can restore trusted service.
So in short, jamming and detected spoofing are not too bad. Undetected spoofing is an unmitigated disaster.
Jamming
Some brief words on jamming. GNSS signals are incredibly weak and are easily drowned out by terrestrial signals, often just by accident. Researchers that investigate jamming have very well calibrated signal generators that aim to only disrupt GNSS within their own testing environment.
Other people that want to disable their vehicle trackers use far blunter methods. This appears to happen a lot in transportation. Such jammers often send out signals that disrupt GNSS within a hundred meters (or more). People doing measurements next to highways pick up these activities easily enough. The galmon.eu network has recorded several instances of this.
Jamming can be mitigated by a host of RF means (see for example here in section “Countermeasures”). One key aspect of actual GNSS satellites is that they broadcast from high above the horizon - unlike most jammers. Special antennas are available that can ’null’ out jamming.
Jamming can easily be detected by looking at the Automatic Gain Control of a receiver. In addition, many receivers will also set a ‘jamming’ flag if they think the signal is wrong.
Note that receivers might get confused by jamming and report wildly wrong locations (See “A study on the accuracy of GPS positioning during jamming”). In that sense, jamming can be a lot like spoofing. Much depends on the receiver.
OSNMA has no role to play in overcoming jamming - it only does authentication of signals that were received correctly.
Spoofing
A receiver needs two things to determine its fix: the exact time of arrival of GNSS signals, plus the digital contents of these signals. The latter turns the former into a fix of position, velocity and time.
To spoof a receiver, we can therefore either mess with the arrival time or with the contents (or both!). OSNMA adds clever digital signatures to the contents, but can not provide protection for the time of arrival (except indirectly).
One of the simplest ways of spoofing a receiver is called ‘Meaconing’, and it is as simple as it is devious. Meaconing works by recording GNSS signals in location A and retransmitting them in location B.
Because of how GNSS works, the delay in getting the data from A to B “falls out of the equation”, and the receiver in location B will now truly believe it is in location A.
The threat of meaconing is real - a ship or drone could be lured into the wrong place, for example. Although there is no proof, it appears a US military drone has been made to land in Iran this way.
Since the navigation messages received are absolutely authentic, a receiver will have a hard time detecting a meaconing attack. OSNMA can play a limited role however (more about this later).
Radio frequency aspects of spoofing
As noted, GNSS signals are very weak, actually weaker than the noise floor. So how does it even work? The GNSS signal we want to transmit (“ones and zeroes”) is multiplied by a block wave with a known pattern. This pattern (PRN) is different for every satellite.
The receiver also knows this pattern, and multiplies whatever it receives with this pattern. If the frequency and phase match with what was transmitted, this multiplication lifts the signal up from the noise. This is exceptionally clever because it 1) allows all kinds of satellites to share one frequency 2) it defeats the noise 3) it gives us information about how far the satellite was away from us (because this influences the phase).
Note that the orbit of the satellite, and the velocity of the receiver, also influence the frequency because of the Doppler effect.
When a receiver does a cold start, it does not yet have an idea at what frequency and phase to expect signals, so it has to start a hunt. Modern chipsets can do this very quickly, though. Once “locked”, the receiver will continue to track a signal based on its known frequency and phase.
Now, this is where it gets relevant - once locked on the actual phase and frequency, this process not only lifts the signal from the noise, it also strongly suppresses other signals that claim to be the same satellite, unless they also come in at the exact same phase and frequency.
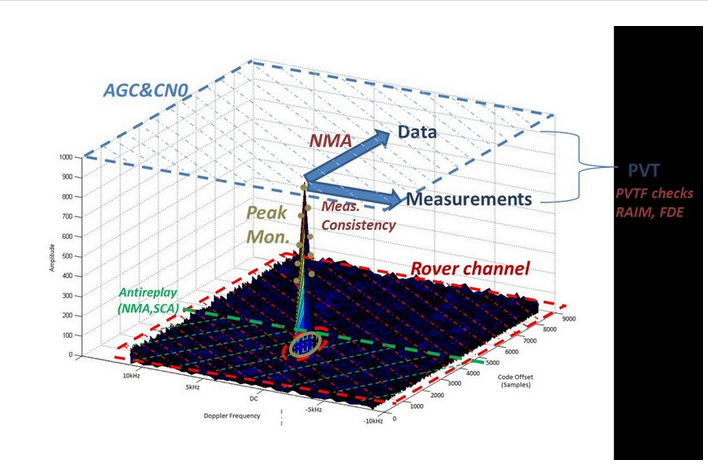
Because of this, it is a lot easier to spoof a receiver from a cold start than it is to spoof a receiver that is already locked. Briefly jamming a receiver might cause it to become unlocked though, so it is vital to detect that too.
What do we want to protect?
There are two distinct scenarios (at least). In one scenario, the operator of the navigation receiver is not considered a threat. This is whenever someone voluntarily uses a GNSS receiver and wants it to work.
In another scenario, the GNSS receiver is tracking the location of heavy vehicles or other rented equipment. This could also be for labour related reasons (maximum number of working hours, resting regulations), or to track valuable loads.
In the first scenario, we are worried about “over the air” attacks, where the spoofer or jammer has no access to the receiver.
In the second scenario, we additionally have to worry about attackers being able to fully shield our antenna, or interrupt the power supply. This might be seen as “over the cable” attacks.
The difference between these two scenarios is large.
Spoofing an operational receiver over the air
If a receiver has been running “unspoofed” for some time, it knows a lot about the world, like where it is, how fast it is going, a very exact indication of the time. In addition, it knows the orbits of around a hundred satellites, from the four major GNSS constellations.
And not only does it know the orbit, it also knows the power, as well as the phases and frequencies of the signals that come in.
As noted above, the RF mechanics already mean that a receiver is set up to reject signals coming in from ‘fake satellites’ that have already been received for real.
All this means that a running receiver has a lot of data that can help it detect spoofing. For example, if the signal strength changes a lot, that is a sure indication the signals are not coming from space anymore.
In addition, an attacker does not know if a receiver is listening to all GNSS and on all bands. If only GPS suddenly reports a new location, but BeiDou does not, that again is a strong indication something weird is going on.
To detect “meaconing”, the receiver could use its own clock. Because although the meaconing technique delivers absolutely authentic navigation messages, it does deliver them with a delay - the time it took to transport the (authentic) signal from A to B. A sufficiently precise clock will pick this up, if this “spoofed distance” is large enough.
Now, an advanced spoofer might be aware of this, and change the transported signals so the time offset is compensated for digitally. And this finally is where OSNMA comes in - OSNMA would pick up this digital manipulation.
OSNMA itself has a complicated relation with time. OSNMA signatures are made using a key that is revealed immediately after its use. A key is tied to the Galileo System Time. If a receiver can be confused on what the time is, it might be made to believe a signature generated using a key that has been disclosed already. OSNMA contains special techniques to prevent this, and this will be detailed in part 4.
One could of course also attempt to spoof a receiver by creating wholly new fake satellites, and having these transmit handcrafted navigation messages that make the receiver think it is somewhere else. Again, OSNMA makes this very hard - not only will there be no valid OSNMA signatures on your messages, the authentic almanac of the GNSS will also deny that your fake satellite exists.
One alternative solution is of course to spoof signals from very low elevation satellites that the receiver has not seen yet. In this way, the reverse effect can be achieved: if the receiver locks on to our ‘fake’ satellite, we can then make it transmit authentic signals, but subtly delayed (or advanced). If we keep this up we can eventually spoof all satellites, and convince a receiver it truly is somewhere else.
It is also possible to very carefully emulate all aspects of the bona fide (locked in) satellite signal and then slowly increase the power and insert doctored data. OSNMA would however detect that the contents of this new signal are not authentic - leaving the attacker only the option to manipulate the timing (somewhat).
Multi-receiver tricks
Which brings us to a very clever analogue way of detecting spoofing. There is a reason GNSS comes from space and needs many satellites. To accurately determine our location means we have to receive signals from multiple angles.
Imagine having not one receiver, but having (say) four, placed in a square. If we ask these four receivers where they are, under normal conditions they’d report they were all in the same plane, on four corners of a rectangle. Specifically, our two receivers to the east would report being closer to satellites orbiting to the east of us. And similarly for receivers to the north, south and west.
Now imagine the situation where someone is meaconing us or otherwise is sending us fake signals. In this case, all four receivers will report being in the same position, but some of them will report a slightly different time. This is because the four receivers have a differing distance to the spoofer’s transmitter. The relative arrival time of the satellites being retransmitted (or faked) does not change depending on our position.
In this way we can very reliably detect we are being spoofed - our multiple receivers all report being in the same place, but they do report (slightly) different times.
In addition, even a single-receiver setup can monitor the polarization of satellite signals (right hand, left hand). Due to multipath signals, real satellites will show a mix of polarization ratios, while a single spoofing antenna will show only one. See “A low complexity GNSS spoofing detection method for vehicular applications” for example.
To beat these simple tricks, a spoofer will need to have multiple transmitters that actually show the same parallax as the actual satellites. However, you can only do this by placing your transmitters next to the satellites - in space. This raises the bar significantly.
Role of the receiver
As noted above, there are many ways for a receiver to detect that it is being spoofed. Every receiver should already perform ‘RAIM’ or Receiver Autonomous Integrity Monitoring which helps detect ‘impossible’ signals, and possibly reject them. This will already prevent simplistic spoofing attempts.
A receiver could however do far more checking, some of which we might reasonably expect it to do. But we have no assurance that it will.
A receiver that really works on it might be nearly impossible to spoof without it knowing about it. For example, it might stringently test against satellites that transmit different data than described in the almanac.
A receiver could also decide that signals from below the horizon are impossible. In addition, since the device already knows where it last was and what time it was then, any changes in location that are “impossible” given the vehicle profile could be rejected. Similarly, a lack of reported movement can be very suspicious for an airplane, but some forms of spoofing look like that.
Signal strengths that fluctuate wildely are also very suspicious.
In addition, receivers differ in their multi-band abilities. Most GNSS satellites now transmit on a lot of different frequencies. Some receivers actually use multiple bands, but do not decode data on all bands. Moving to doing so again raises the bar on a spoofer - it might now have to spoof 8 different signals.
It is also possible to download live satellite orbit information over the Internet (“assisted GPS”). This can also be checked against what is being received over the air.
In my experience, most manufacturers ship software that superficially performs the expected functions, but most vendors do not then “go the extra mile” to deliver features the user wasn’t aware they needed. So my expectations aren’t very high for how hard today’s (commodity) receivers work to detect spoofing.
It should also be realised that any form of spoofing detection will lead to false positives. Multipath signals for example could easily be confused for spoofing, and these happen a lot.
Some thoughts
We’d love to have technology that would protect us againt all threats, from all opponents, all the time.
With pure cryptography, we can sometimes approach this goal. For example, from a mathematical perspective, AES looks to be extremely solid against all threats. Incidentally, one of the two inventors of AES also helped design OSNMA.
OSNMA and GNSS receivers can in no way approach this “absolute security level” of AES. A clever attacker with large amounts of resources could indeed successfully spoof a receiver by very carefully taking existing, fully signed, navigation messages and replaying them with the tiniest of delays.
Incidentally, AES (and most cryptographical algorithms) are vulnerable to the reverse - it turns out that the time (and/or power) they take to encrypt a message can depend on the relation between the key and the message. If you can measure encryption operations real closely this can sometimes allow you to recover the key.
Given that we can’t reach absolute security under all circumstances, we should focus on raising the bar. This can happen in terms of sophistication and money required for hardware, or it can happen by making a successful attack take a lot of time and skill.
Simple “raising the bar exercises” were mentioned above: using as many GNSS signals as possible, checking them carefully against the almanac, verifying the signature on all signals (when these become available), reject “impossible” changes in position and time, reject signals you should not be able to see, alert on signal strength changes, try to keep a receiver locked at all times. But much more could be done.
OSNMA is a nice addition to the palette of possibilities, specifically because it makes it very hard for a sophisticated attacker to paper over delays by fiddling with the navigation message. But it should be noted that ONMA is only one part - it can’t solve the problem on its own.
OSNMA might have a special role to play in receivers where the attacker has the ability to sit right next to the antenna. Very simple replay attacks that work on current generation receivers would be rejected out of hand by an OSNMA capable receiver with even a moderately correct clock.
This is especially important since a receiver in an uncontrolled environment can not rely on the ‘4 antennas’ trick outlined above - the attacker could spoof each of them individually easily enough.
Summarising
The most important thing for a receiver is to not be spoofed without knowing it. There are many things a receiver could do detect a spoofing attempt, some physical, some software, some cryptographic (OSNMA). OSNMA has a role to play in detecting and preventing some attacks, but it is only part of the arsenal. Much depends on how clever a receiver wants to be to detect spoofing, and expectations for most receivers should be limited on this front.